The crucial link between cyber security and operational technology
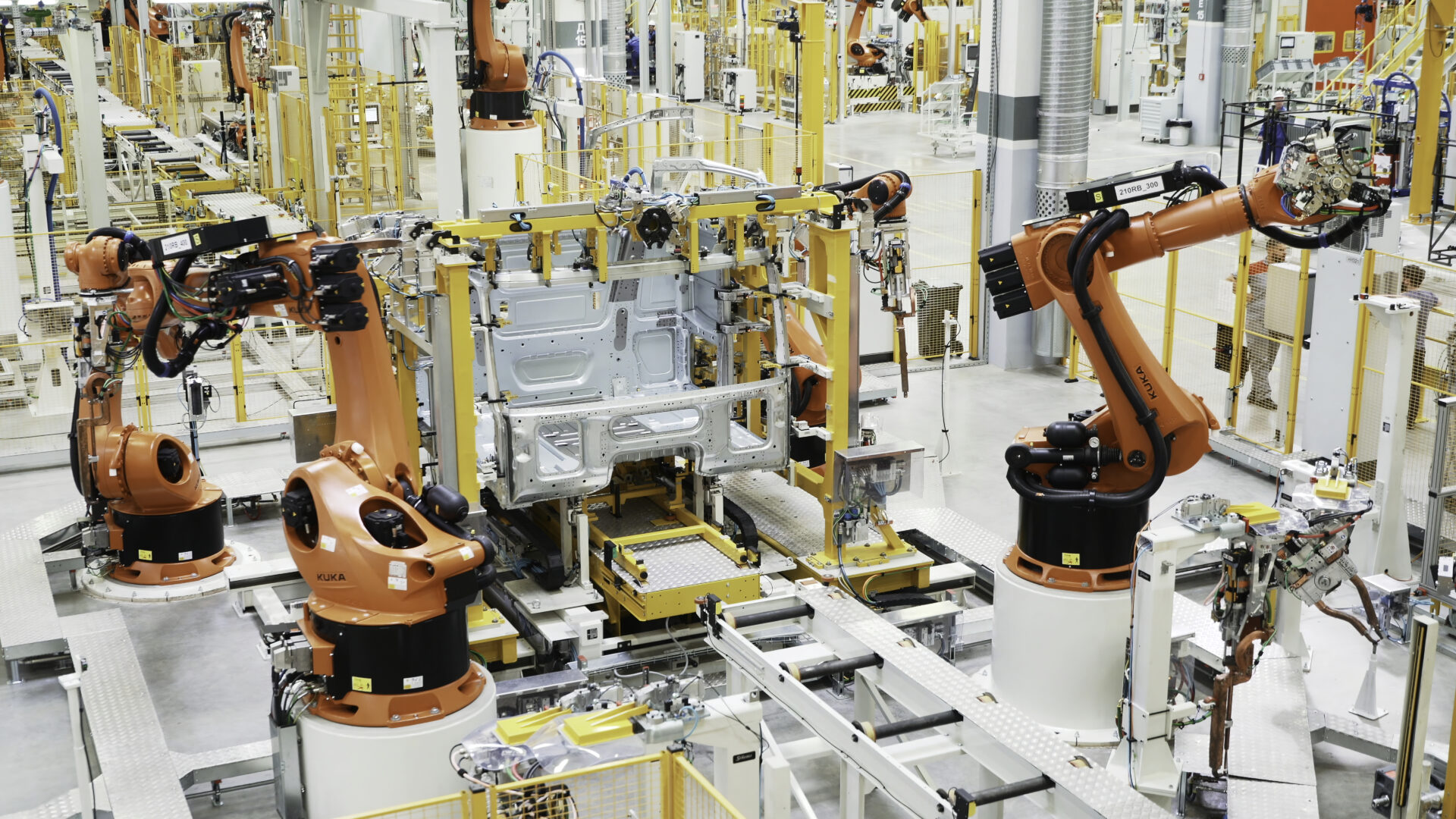
Running through the veins of industrial operations lies Operational Technology (OT). OT systems—comprising hardware and software—play an increasingly pivotal role in monitoring and controlling physical devices, processes, and critical infrastructure. However, with this reliance comes a pressing concern: security. In an era where cyber threats continually change shape, safeguarding OT systems is not just a priority—it is an imperative.
OT encompasses a diverse array of hardware and software tailored specifically for industrial settings. From sensors and controllers to supervisory control and data acquisition (SCADA) systems, OT forms the backbone of manufacturing, energy production, transportation, and beyond. But as these systems become more interconnected and integrated with traditional IT networks, the risk landscape expands exponentially.
The role of cyber security companies
The advent of IT/OT convergence brings forth both challenges and opportunities. On one hand, it fosters seamless data exchange and operational efficiency. On the other, it exposes OT environments to a myriad of cyber threats previously confined to the realm of IT. Cyber security companies are at the forefront of this battle, devising innovative solutions to fortify OT systems against evolving threats.
Retrofitting for resilience
Ease of installation is paramount in the integration of cyber security measures within OT environments. Traditional security solutions often fall short in this regard, requiring extensive customisation and downtime. However, modern cyber security firms are addressing this issue head-on by developing user-friendly solutions tailored specifically for OT infrastructure. Streamlined deployment processes minimise disruptions while ensuring robust protection from cyber intrusions.
Retrofitting cyber security measures onto existing OT networks presents its own set of challenges. Legacy systems, characterised by outdated protocols and proprietary technologies, pose a significant barrier to effective cyber security implementation. Cyber companies are employing adaptive strategies to overcome this hurdle, offering tailored solutions that seamlessly integrate with legacy infrastructure. By leveraging advanced threat detection mechanisms and anomaly detection algorithms, these solutions fortify aging OT systems without compromising functionality or performance.
Quantum-safe encryption: future proofing OT security
The integration of quantum-safe encryption (or post quantum cryptography) represents a pivotal step towards future-proofing OT security. As quantum computing inches closer to reality, conventional encryption methods face unprecedented vulnerabilities. Recognising this impending threat, cyber security firms are pioneering quantum-safe encryption technologies designed to withstand the computational power of quantum adversaries. By adopting these innovative encryption protocols, organisations preemptively shield their OT assets from future cyber onslaughts, ensuring resilience in the face of technological upheaval.
Despite these advancements, a critical gap persists—visibility. The SANS Institute’s study, “Breaking IT/OT Silos With ICS/OT Visibility,” underscores the pressing need for enhanced visibility into OT assets. The study reveals a staggering statistic: more than half of surveyed security leaders cite insufficient OT training as the primary limitation in improving Security Operations (SecOps). Bridging this gap requires an integrated approach, encompassing comprehensive training programs, cross-departmental collaboration, and innovative technological solutions.
Cyber security companies are rising to the occasion, offering specialised training modules tailored for IT professionals venturing into the realm of OT security. By equipping personnel with the knowledge and skills necessary to navigate the intricacies of OT environments, these training initiatives bolster organisational resilience and foster a culture of proactive cyber security vigilance.
In the dynamic landscape of industrial cyber security, the importance of securing operational technology cannot, and should not, be overstated. As OT systems converge with IT, the need for robust defenses becomes ever more pressing. Fortunately, cyber security companies are rising to the occasion, offering tailored solutions that address the unique challenges of industrial environments.
From ensuring ease of installation to retrofitting existing networks and pioneering quantum-safe encryption, these companies are at the vanguard of OT security. By partnering with them, organisations can safeguard their operations, protect critical infrastructure, and embrace the opportunities of digital transformation with confidence.
Article written as part of techUK’s Operational Technology Security Impact Day – 15 April 2024
- CyberHive announces groundbreaking €4.9m EU project
- How Do I Get Ready for Post-Quantum Cryptography?
- Why Quantum threats are closer than you think (Should I be worried about Post-Quantum Cryptography now?)
- What Exactly is Post-Quantum Cryptography (and Why is Everyone Talking About It)?
- Is AI a Threat to Your Business? Cyber Solutions to Ensure Protection
Get in touch
If you have a question or would like some more information, contact us today.