What is post-quantum cryptography and why you need it
When we talk about post-quantum cryptography we are referring to the development of quantum-safe cryptographic systems for traditional computers. This will enable those computers to defend against attacks from quantum computers. We are not yet in the age of quantum computing. However, when it arrives, it could be revolutionary – yet devastating if used in the wrong way.
What is quantum computing and why does it matter?
A quantum computer is essentially a computer that is able to take advantage of the properties of quantum mechanics, including superposition and entanglement. Quantum computers will be able to carry out calculations that could have taken a binary computer years to complete in a matter of hours. There are many potential consequences and benefits of this but one of the key challenges to note is that a quantum computer will likely be able to quickly break algorithms that have been used for public key encryption. That is one of the main reasons for the investment of time and money in post-quantum cryptography – to defend against this encryption attack.
Quantum-resistant algorithms
Today’s computer cryptography uses mathematical equations (algorithms) and secret keys to encrypt and decrypt data transmissions over a computer network or the internet. These algorithms are secure enough against decryption attempts using traditional computers. Quantum computers are much more powerful and stand to solve problems at a rate incredibly greater than our traditional computers.
Currently, the internet runs on RSA2048 public key cryptography – encryption that would take 13.7 billion years to break using a conventional computer today. Using a Quantum computer, researchers have calculated this would take just 42 minutes to crack. Fundamentally, everything from web browsing, email, financial transactions, online shopping, and even cryptocurrency could be put at risk.
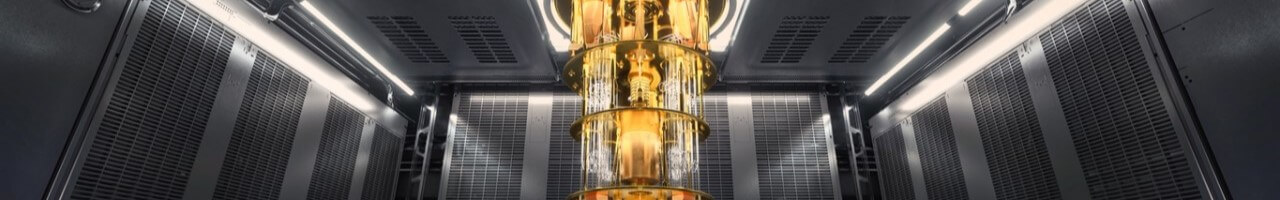
IBM have made rapid progress in developing quantum computing over the past few years, with real quantum hardware now available to thousands of developers. Further to this, there are experiments in post-quantum cryptography in action all over the world today. This stands as a testament to both understand and protect ourselves from quantum computing.
Post-quantum cryptography
Currently, the generic algorithms that we use for everything, from ecommerce through to defence, are considered to be safe. However, that will all change as soon as quantum computing breaks into the mainstream. The quantum-safe communities best guess is that quantum computing will be widely available in just over six years. Technology has a history of advancing rapidly, so don’t wait to prepare for quantum.
When our existing cryptography is no longer considered secure in the way that it is today, a whole range of sensitive data will suddenly be at risk. That’s why cyber security teams need to be focused on post-quantum cryptography. This cryptography is the foundation of our response to the risks of quantum computing, and will define data security going forward.
Become quantum-safe
With the importance of post-quantum cryptography understood, it is also important to begin protecting yourself now. CyberHive Connect offers quantum-safe cryptography, alongside many other features such as zero trust network access and enhanced privacy (VPN alternative). It does this all whilst being simple and scalable.
We’re proud to offer this product on a personal license for free. Our team of experts are just a few clicks away if have any questions or need assistance.
- CyberHive announces groundbreaking €4.9m EU project
- How Do I Get Ready for Post-Quantum Cryptography?
- Why Quantum threats are closer than you think (Should I be worried about Post-Quantum Cryptography now?)
- What Exactly is Post-Quantum Cryptography (and Why is Everyone Talking About It)?
- Is AI a Threat to Your Business? Cyber Solutions to Ensure Protection
Get in touch
If you have a question or would like some more information, contact us today.